This summary is not available. Please
click here to view the post.
WHAT'S NEW?
Loading...
Today, we commonly find wireless networks around us. Most wireless
networks are encrypted using WEP or WPA encryption methods. In a
previous post dictionary attack on WPA networks. In this post, I'll cover WEP which has weak mechanism, thus easy to crack, compared to WPA and WPA2.
Theory
WEP, short for wired equivalent privacy, is one of several encryption schemes used to secure wireless networks. At the time of conception, WEP was believed to be secure. However, a security flaw was found in the IV headers of data packets that makes it possible to crack WEP if enough IV headers are collected. The attacks shown in this tutorial take advantage of this weakness in the initialization vectors of wireless packets to crack WEP.When enough packets have been collected, the key for the WEP-secured network can be cracked by using wifi-hacking tools, such as aircrack-ng. Kali Linux includes aircrack-ng among one of its top 10 security tools for testing vulnerability of computer networks. In this post, I'll demonstrate how a WEP key can be easily found using the aircrack-ng tools in Kali Linux. However, a problem may arise when there are multiple keys in use instead of just one.
What You Need To Follow The Steps In This Tutorial
You need Kali Linux and basic knowledge of Linux. Kali Linux is a Debian-based Linux distribution for testing network security. Kali Linux currently supports PC's and ARM-powered machines. If you use a PC, download the Kali Linux ISO and burn it to a black DVD with InfraRecorder or another tool.Then, boot your computer with the Kali Linux DVD. Hopefully, you'll be automatically presented with a nice and dark GUI screen of GNOME desktop. For information on running Kali on ARM hardware, see this page.
Let's Crack WEP
- Open the GNOME Terminal (the square icon with >_) and type the
command for loading a driver for your wireless network card or USB WiFi
adapter. You may have to put required firmware in /lib/firmware before
trying to load the driver because Kali Linux lacks firmware for some
drivers. For example, to load b43 driver, type:
modprobe -r b43 modprobe b43
If the WiFi driver is working, then the network traffic in the top right corner of the screen will show available wireless networks when you click on it.
- Use kismet to find information about the WEP-secured wireless network that you want to crack. This post shows you how. You need such information as:
- Name of the wireless network (ESSID)
- MAC address of the access point (BSSID)
- Channel of the wireless network
- MAC address of wireless clients
- Type the following commands to put your wireless device wlan0 in monitoring mode.
airmon-ng stop wlan0 airmon-ng start wlan0
- Change the MAC address of your wireless network card. This
may or may not work depending on the hardware used. In the example, the
text in red is the new MAC address for
your wireless card. Usually, this MAC is the actual MAC address of an
existing wireless client associated with the target network. With the
fake MAC, we're going to trick the access point with one of the
following attacks.
ifconfig wlan0 down ifconfig wlan0 hw ether 6C:83:36:6C:65:CD ifconfig -a - Start airodump-ng which will sniff wireless traffic of the
target network and collect good IV's (initialization vectors, part of
WEP encryption data). The logfile will be used later to find the WEP
key. The number after -c option is the channel
of the wireless network to listen to. The screen will show wireless
networks and associated clients, if any, with a set of numbers
increasing. Don't stop airodump-ng or close the terminal yet. Just leave
the terminal open.
airodump-ng -w logfile -c 6 --ivs wlan0 - In the following attacks, we are going to use aireplay-ng.
Aireplay-ng is a handy tool for generating more wireless traffic in
order to collect sufficient amount of good IV's. It does so by injecting
or replaying captured packets to fool the access point into giving us
what we need. Open another tab in GNOME Terminal. This attack will
associate the target wireless client with the access point.
aireplay-ng -1 30 -e WIFINET -a 00:23:97:26:66:A3 -h 6C:83:36:6C:65:CD wlan0
The -e option specifies the network name, the -a option specifies the MAC address of the AP, and the -h option specifies the MAC address of the wireless client. You can use macchanger to view and change your MAC address, for example,macchanger -s wlan0. Then, you can associate your wireless adapter when there are no clients connected to the wireless network in the first place.
- ARP injection is slow but always works. While airodump-ng is
listening, open another tab in GNOME Terminal and start the ARP
injection attack.
aireplay-ng -3 -b 00:23:97:26:66:A3 -h 6C:83:36:6C:65:CD wlan0
The -b option specifies the MAC address of the AP and -h specifies MAC address of the associated client. Let it run and airodump-ng will pick up traffic. If no client is connected, we can create one by fake authentication described above.
- This attack generates traffic by asking the access point to
resend data packets. Open another tab in GNOME Terminal and start the
interactive packet replay attack.
aireplay-ng -2 -b 00:23:97:26:66:A3 -h 6C:83:36:6C:65:CD -n 160 -p 0841 -c FF:FF:FF:FF:FF:FF wlan0
The -b option specifies the MAC address of the AP and -h specifies MAC address of the associated client.
- After enough packets have been collected and saved, aircrack-ng can be used to crack the WEP key.
aircrack-ng -a 1 -b 00:23:97:26:66:A3 -n 64 logfile-01.ivsReplace the filename with your log file that was previously generated with airodump-ng. Also, specify the access point's MAC address with -b option. The -n option specifies whether the WEP strength is 64-bit or 128-bit. The -a 1 option specifies that we're cracking WEP.
If you still can't crack WEP with tons of IV's, increase the fudge factor with -f N option (N>=2). It'll take much longer to crack but you'll have a better chance at success.
How to solve the error “404 Not Found” during Kali Linux updates:
While updating a new installation of Kali Linux, I received the error message
Apparently, the hostname http.kali.org points to a CDN and not all of its mirrors contain updated packages. In order to solve this I went to the Kali mirror list and chose another mirror from my continent. I then updated the file /etc/apt/sources.list accordingly (replace with your chosen mirror):
Finally, update the package database, then try to upgrade Kali Linux again:
While updating a new installation of Kali Linux, I received the error message
Err http://http.kali.org/kali/ kali/non-free metasploit amd64 4.8.2-2014012201-1kali0 404 Not Found.Apparently, the hostname http.kali.org points to a CDN and not all of its mirrors contain updated packages. In order to solve this I went to the Kali mirror list and chose another mirror from my continent. I then updated the file /etc/apt/sources.list accordingly (replace with your chosen mirror):
- Uncomment this line:
#deb http://http.kali.org/kali kali main non-free contrib - Insert line with the mirror URL below:
deb http://mirror.pcextreme.nl/kali kali main non-free contrib
Finally, update the package database, then try to upgrade Kali Linux again:
apt-get updateapt-get upgrade
Simple question, hopefully a simple answer:
it is an Information Security discipline where the aim is to identify
ways to compromise you and/or your organisation. There is more to it
than that, obviously, but that should provide a good starting point!
Many people involved in the industry, such as penetration testers, sales
people, information security consultants, etc. all have their own
interpretation of penetration testing, and there is a wide ranging view
of what it is and how to go about it. Frustratingly, these differences
in opinions of what constitutes a pen test often leads to it being
mis-sold and, more commonly, not conducted correctly. Both actions
result in a negative attitude towards penetration testing which results
in many objections or reluctance to carry it out, ultimately meaning
people are losing out in the value a penetration test gives.
Solutions, problems, needs
Penetration testing is a part of a solution to a problem. The
problem is that there are various threats out there that can affect the
security of your information. We occasionally hear: “Who would want my
information? It is of no value to anyone else but me.” Now, in a very
small set of circumstances that may be true. However, in the majority
of cases, there is always someone out there that can benefit in some
manner from obtaining or destroying the information you have. This
someone could be identity thieves, your competitors, foreign
governments, discontented staff, hacktivists, online vandals, the list
goes on. A penetration test should be focussed on replicating threats
that are relevant to your organisation. A foreign intelligence threat
may be very high on the list if you are a government body but not so
much if you are a retailer, for example. It is this understanding of
the threats that should form and drive a penetration test.
Pen testing is not just about using a collection of tools and
scripts, it is also a mentality. Whilst at Perspective Risk we train
our team how to use all the tools at their disposal, we also teach them
when and where to use them. We believe this brings more value to our
customers and differentiates us from the one size fits all approach
offered by other organisations, either through their pen test led
approaches or through their automated “appliances”. Now, we are not
saying there is no place for these approaches; we are saying that these
approaches address specific needs but may not help in solving the
problem. Problem? Need? What’s the difference? A problem is something
you have, but don’t want, a need is something you want but don’t have.
Needs should be derived from problems, quite often the two are
considered the same which can lead to unwanted results. What we ask is:
how can a pen test address a need where the need does not address the
problem?
Value Proposition
So, what value does penetration testing give you? Well, in some
people’s opinion, where you have been mandated to get one done, it gives
you a tick in the box. Is that all we think a penetration test gives
you? Definitely not! There is much more value gained from a pen test
that is often not even contemplated. We hope to correct that!
Beyond the tick in the box you get for whatever regulation,
compliance, or legal requirement you are aiming to meet, penetration
testing actually reduces overall costs, brings certainty, and allows you
to prioritise your resources. Oh, we almost forgot, it increases the
security of your organisation.
How does it save you money? Well, what is cheaper?
Pro-actively implementing known fixes where you have control over time
and resources, or fire fighting a security breach? Comparing the two
scenarios, on the one hand where you have taken a pro-active approach,
you can blend in the fix requirements to either your own staff’s day to
day activities or in to contracts where you outsource the service,
usually at no additional cost. If a breach occurs, instantly the
priority turns to fixing the issue, money, time and people will be
thrown at the problem. This could result in extra costs for overtime,
extra contract staff or external services. Similarly, the fire fighting
activity may not be included in your service agreement with your vendor
and therefore would result in extra charges for out-of-agreement
requirements. There are also hidden costs that are often not thought
about; for example, while all these resources are fire fighting, they
are not actually doing what they were originally paid to do. Your
operations are likely to suffer and that subsequently affects your
efficiency or your income.
How does it bring you certainty? The results of a
good penetration test are black and white. If they are not, you should
look for another supplier! They are meant to give you a perspective on
your technical risk. They are meant to provide you with a customised
view of the threats you face and the risks that are relevant to your
organisation. Knowing that the issues found are real and relevant to
your organisation gives you certainty about how vulnerable you actually
are to the threats that matter to you the most. It gives you a defined
set of fixes and removes false positives that are becoming more and more
prevalent due to the commoditisation of penetration testing.
How does it allow you to prioritise? In most
organisations, and certainly in this time of austerity, we are being
asked to produce more with less. That is to say, more is expected
whilst resources such as time, money, and people are increasingly
limited. In this environment, you really have to prioritise to get
things done. The issues that are found in a pen test are ranked by the
severity and the threat of the technical risk in a pen test report.
This allows you to give precedence to the more severe issues as opposed
to deploying resources on issues that do not present a great risk to
your organisation.
How does it make you more secure? This one is
fairly simple. A pen test finds holes that your threats may use and
these are then reported to you with advice on how to go about fixing
them. Once you plug the gaps, the security of your information is at a
greater level than it was before the pen test. Usually, information
security consultancies that provide penetration testing as part of many
InfoSec services only answer this question as they don’t understand the
full value proposition of a penetration test. It is why we recommend
utilising specialist penetration testing consultants, where the quality
and understanding runs through not just the consultant but through the
entire company.
Most of the time when you see Kali-Linux tutorial on YouTube, you will find the custom background text on the terminal. it,s looking very interesting.
Today i am going to show you How to Change Background Text in Kali Linux Terminal ?
| root@Kali:~# apt-get install figlet |
now go to the File System and open the etc folder.
now Search for bash.bashrc file and open with the Leafpad .
now enter the figlet “Yourtext” and save it.
now open the terminal, your custom text is there on the terminal.
Kali Linux is becoming popular and more and more users are using it
to try out different things. When installing kali, you get to choose a
hostname, but in case you accepted the default hostname (kali) and later
want to change it, here’s a How to guide to change hostname in Kali
Linux.
Now just changing hostname to something else might not be enough. How
about we change hostname every time you boot your computer to a random
one? That could be fun. It also helps to avoid suspicion from System
Admins in your network to see “kali” in their network. Like BackTrack,
SysAdmins doesn’t like Kali much (I mean why would they? Kali is
designed to poke and prod around the network to find vulnerability).
Even if you’re using Kali as your primary OS, it just raises eyebrows
and you might get a visit from an over-conscious SysAdmin. So we will
discuss all possible ways, change hostname to something else permanently and change hostname randomly in each boot.
- Change hostname permanently and make it sticky – with reboot
- Change hostname permanently and make it sticky - without rebooting
- Change hostname randomly in each boot time.
Change hostname permanently – with reboot
Step 1: edit hostname file
Open hostname file from /etc directory and modify the name in there.
leafpad /etc/hostname
Let’s say we change the name from kali to aiur
Save the file.
Step 2: edit hosts file
Open hosts file from /etc directory and modify the name in there.
leafpad /etc/hosts
Change kali to aiur.
Save the file.
Step 3: reboot
Now reboot to reflect your changes
reboot
And you should see the new
hostname coming up in terminal (i.e. root@aiur)Change hostname permanently – without reboot
Don’t want to reboot? Here’s how
Follow step 1 and 2 from above
i.e.
- Update
/etc/hostname - Update
/etc/hosts, so local address (es) resolves with the new system name.
Reload configuration files
Type in following 3 commands one at a time.
service hostname.sh start service networking force-reload service network-manager force-reload
Now force-reload networking service.
This will temporarily disconnect your system from the network (ssh usually resists short disconnection)This might definitively disconnect your system from the
network because networking might not restore connections; please reboot,
which is not lazy, but ensures that your setup is really correct
So we need to reload network-manager service as well.
This should reconnect networking again.
Depending on what other services you’re running, i.e.
avahi, metasploit, postgresql, cups, openSSH server, ssmtp etc. you might have to restart them all.
Now you must close your existing terminals to have the new hostname
coming up at the top. See following screenshot with highlighting.
First screenshot is after re-loading all the required services. Note that it’s still showing root@kali in the top.
uname -a or hostname shows correct info though.
If I close this terminal and open a new one, root@kali becomes root@aiur which is what we want.
Change hostname randomly in each boot time
Following procedure will allow you to change your hostname randomly in each boot. That hostname will stick until you reboot again.
Create a bash script
Create a script which will automate the procedure
In this terminal create a file.
touch newhostname leafpad newhostname
Now, add the following lines to your newly created file:
#!/bin/bash
cp -n /etc/hosts{,.old}
idomainname=$(domainname -i)
fdomainname=$(domainname -f)
newhn=$(cat /dev/urandom | tr -dc 'A-Z' | head -c8)
echo $newhn > /etc/hostname
mv /etc/hosts /etc/hosts.old
echo "127.0.0.1 localhost" > /etc/hosts
echo "$idomainname $fdomainname $newhn" >> /etc/hosts
echo "# The following lines are desirable for IPv6 capable hosts" >> /etc/hosts
echo "::1 localhost ip6-localhost ip6-loopback" >> /etc/hosts
echo "ff02::1 ip6-allnodes" >> /etc/hosts
echo "ff02::2 ip6-allrouters" >> /etc/hosts
service hostname.sh stop
sleep 1
service hostname.sh start
service networking stop
sleep 1
service networking start
service network-manager stop
sleep 1
service network-manager start
xhost +$newhn
exit
Save it and exit leafpad.
Note: I’ve used only CAPS here for new hostname,
'A-Z'. You can also choose a mixure of uppercase and lowercase ('A-Za-z') or numbers etc.
Also I’ve chosen 8 characters long hostname
head -c8, you can change it to any length you like.Move script to /usr/bin/ folder
We need to move this file to
/usr/bin.mv newhostname /usr/bin/newhostname
Make it executable
Use the following command to make
newhostname file executable.chmod +x /usr/bin/newhostname
Make it run at Startup:
Now that we have the script in right place and it’s executable, we
need to add it your Startup applications. This will allow your system to
run it every time you reboot your machine and generate a new hostname for you.
Follow the steps below:
Follow the steps below:
- Click on “Applications” –> “System Tools” –> “Preferences” –> “Startup Applications”
- Click “Add”
- Fill in:
- Name: Random Host Name
- Command:
/usr/bin/newhostname - Comment: Start Kali with a random hostname each boot
- Click Save
- Close Windows
Reboot
Finally reboot your machine to load the script at start-up.
reboot
Enjoy your new
hostnames. File Operations
pwd Print Name Of Current/Working Directory
cd Changing The Working Directorycp Copy Files Or Directory
rm Remove Files And Directory
ls List Of Directory Contents
mkdir Make Directory
cat Concatenate Files And Print On Standard Output
mv Move Files
chmod Change Files Permissions
Know Your System
uname Print System Information
who Show Who Is Logged On
cal Displays Calculator
date Print System Date And Time
df Report File System Disk Space Usage
du Estimate File Space Usage
ps Displays Information Of Current Active Processes
kill Allows To Kills Process
clear Clear The Terminal Screen
cat /proc/cpuinfo Cpuinfo Display CPU Information
cat /proc/meminfo Display Memory Information
Compression
tar To Store And Extract Files From An Archive File Known As Tar File
gzip Compress Or Decompress Named Files
Network
ifconfig To Config Network Interface
ping Check The Other System Are Reachable From The Host System
wget Download Files From Network
ssh Remote Login Program
ftp Download/Upload Files From/To Remote System
last Displays List Of Last Logged In User
telnet Used To Communicate With Another Host Using THe Telnet Protocol
Searching Files
grep Search Files(s) For Specific Text
find Search For Files In A Directory Hierarchy
locate Find Files By Name
CodePrecode
You can now install Kali Linux on any Android Phone or Tablet. Pre-requisite to install Kali Linux is here below.
- OS version: Android 2.0
- Memory: 5 GB free
- Fast wireless connection
- Patience to wait for distribution and boot from the network
Please click here to follow the steps. Than

Tor (used to stand for "The Onion Router", but it's no longer considered an abbreviation, so it's just "Tor"), is an anonymity network, used to surf the web (and more) anonymously. Basically, anyone running the Tor software on their computer runs a proxy, and traffic gets passed (encrypted) from one person running Tor to another person running Tor, multiple times through many users, until it get's to the page that you requested. Hence the term "Onion" used to describe it, since it works in "layers". Each person running Tor on their computer is called a "Node".
To the page (and anyone logging requests to that page, such as the website owner for example) they can only see the IP address of the last Node (called the "end node"). Any communication along the way, between you, when you request the website page, and the final destination, is encrypted, and cannot be analyzed. However, the last Node in the chain can log and view traffic through it, if the person running it is unscrupulous, so for that reason it can't be said that Tor is 100% anonymous.
TOR Auto-install Bash Script
#!/bin/sh
echo "deb http://deb.torproject.org/torproject.org wheezy main" >> /etc/apt/sources.list
clear scr
echo "[*] Installing the keys...."
gpg --keyserver keys.gnupg.net --recv 886DDD89
gpg --export A3C4F0F979CAA22CDBA8F512EE8CBC9E886DDD89 | sudo apt-key add -
echo "Ready!!"
clear scr
echo "[*] Updating Repositories...."
apt-get update
clear scr
echo "[*] Installing TOR"
apt-get install deb.torproject.org-keyring
apt-get install tor
echo "Ready!!"
echo "[*] Installing Vidalia"
apt-get install vidalia
echo "Ready!!"
echo "[*] Installing iceweasel-torbutton"
apt-get install iceweasel-torbutton
echo "Ready!!"
clear scr
echo "[*] Installing Privoxy"
apt-get install privoxy
echo "[*] Configuring privoxy"
echo "forward-socks5 / 127.0.0.1:9050 ." >> /etc/privoxy/config
echo "Ready!!"
service tor restart
service privoxy restart
echo "Tor has been installed successfully."
Save this script to a file like torinstall.sh and chmod +x it.
#chmod +x torinstall.sh
#./torinstall.sh
To install Compiz you need to modify sources.list. This file is located in /etc/apt/ directory. Open sources.list in a leafpad editor or any other text editor and add these lines
## SID: to get compiz
deb http://ftp.us.debian.org/debian/ sid main non-free contrib
Now open root terminal window and type
apt-get update
apt-get -t sid install compiz
you are done installing Compiz
SET stands for Social Engineering Toolkit, primarily written by David Kennedy(ReL1K). The
Social-Engineer Toolkit (SET) is specifically designed to perform
advanced attacks against the human element. SET was designed to be
released with the http://www.social-engineer.org
launch and has quickly became a standard tool in a penetration testers
arsenal. The attacks built into the toolkit are designed to be targeted
and focused attacks against a person or organization used during a
penetration test.
To start SET, either you go to Applications --> Kali Linux --> Exploitation Tools --> Social Engineering Toolkit --> se-toolkit. (This command was valid till Kali Linux ver. 1.0.4, now it changed to setoolkit in Kali Linux ver 1.0.5 and 1.0.6).
or else, open terminal window and type se-toolkit (for Kali Linux ver. 1.0.4) or setoolkit (for Kali Linux ver. 1.0.5 and 1.0.6). When you type this root terminal window, following are steps SET perform
- it will set new config environment
- check for SET software update
- verifying the software
- start SET Menu

SET is a menu driven based attack system, which is fairly unique when it comes to hacker tools. The decision not to make it command line was made because of how social-engineer attacks occur; it requires multiple scenarios, options, and customizations. If the tool had been command line based it would have really limited the effectiveness of the attacks and the inability to fully customize it based on your target.
WPScan is a WordPress
vulnerability scanner written in ruby, which is capable of detecting
common security vulnerabilities as well as listing all plugins used by a
website hosting WordPress. WPScan is pre-installed in Kali Linux.
WPscan is a nice tool if you want to find out how to exploit a WordPress site as it does all of this:
- Username enumeration (Checks the ‘author’ query-string and the location header).
- Weak password cracking (This can be multi-threaded and supplied a password list of your choosing).
- Version enumeration (Finds what version of WordPress they are running by checking meta tags and client side files).
- Vulneralbility enumeration (Based on what version they are running).
- Timbthumb file enumeration (Checks for Timthumb exploit).
- Plugin enumeration (See what plugins they are running).
- Plugin vulneralbility enumeration (Tells you which, if any, plugins are vulnerable to exploits).
- Theme enumeration (What theme are they running. Sometimes you can find exploits in the theme).
- Readme.html enumeration (Sometimes can be useful because you will see what is needed for that theme. Helps you find out what they are running. E.G. “This theme require PHP 5″).
- Directory listing (Helps footprint the WordPress installation).
To start WPScan, click on Applications--> Kali Linux--> Web Applications--> Web Vulnerability Scanners--> wpscan
Now, to scan for wordpress plugin to exploit, let pickup any wordpress plugin, ex.: http://www.cretan-snails.com. Type in the root terminal window;
root@kali:~# ruby /usr/bin/wpscan --url http://www.cretan-snails.com
(A)
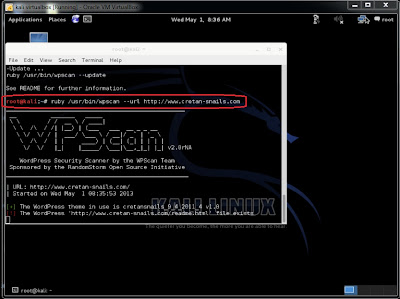
(B)

From the above screenshots, we found that there is 1 vulnerability and 13 plug-ins from passive detection. To find Wordpress usernames, type root@kali:~# wpscan --url http://www.cretan-snails.com --enumerate user
(C)


LazyKali
is an awesome script written in bash shell. It can automate the whole
update and install new tools in your hack repository. As the name
suggests, you can get all the updates on Kali Linux and your
repositories in one place by running this script. Please read the
description of the project here to know what tools are there that are going to be added when you run the script. Download lazykali.sh.
* Warning: Disable firewall or Internet Security application if your Kali Linux is installed in a virtual machine.
To install the script on Kali Linux, run
- rootkali:~#./lazykali.sh on root terminal window. (If you get a message Permission Denied, then first type rootkali:~#chmod +x lazykali.sh and then rootkali:~#./lazykali.sh).
- if the script is not installed it may prompt you to install. Type Y to install the script
- Once the script is installed, it will check the version. If the version is old, allow it to update by typing Y.
- Once execute, you will get a command line interface. Check the below screenshot of the tool.
- If Kali Linux is not updated, then type 1 to update Kali Linux. Once it is updated, type 6 to check available tools that LazyKali offers you.
- Type 3 to install Hackpack. It will prompt you to install Hackpack. Type Y to install Hackpack.
- Now click on Applications on the top left corner of Kali Desktop and you will find Hackpack tab.
The advantage of LaziKali is
that you can modified the code and add some extra tools to this script
to save time and effort. Please find the source code: https://code.google.com/p/lazykali/source/browse/lazykali.sh
Source: kali4hakers.blogspot.in
Source: kali4hakers.blogspot.in
How to reset root password in kali linux ? Now i will show you how to do that :)
Firstly >
1. Boot the machine and wait until GRUB Boot Loader comes up. Select recovery mode and then press e to edit.
Firstly >
1. Boot the machine and wait until GRUB Boot Loader comes up. Select recovery mode and then press e to edit.
2. Change the permission mode from ro to rw and modify boot loader file in init=/bin/bash and then F10 make the changes and reboot the system.


3. Once the system reboot, shell prompts you for the password to manage the system. Type passwd root and then type the desired password of your choice. Confirm the password and then hit enter. If new password and retype new password matches correctly, then you will get the message password updated successfully. Type shutdown -h now to press power button to shutdown the system and then boot the system again.


4. Type root and the new password. If you type the new password correctly, then you will desktop screen of Kali Linux.




























